Executive summary
Anthropic's Claude Mythos Preview represents a genuine inflection point in cybersecurity — not another incremental AI model, but the first system capable of autonomously discovering and exploiting zero-day vulnerabilities at scale across every major operating system and browser. Security leaders cannot afford to treat this as routine.
This HCLTech POV makes the case that organizations must move now — not to rebuild their security programs from scratch, but to recalibrate them for a world where the economics of offense have shifted fundamentally. The attacker's edge is no longer time or expertise. It is automation.
What has changed — And why it matters
The attacker's advantage is no longer skill
For decades, the most sophisticated cyberattacks required rare human expertise. Nation-state actors and elite threat groups dominated advanced exploitation because finding and weaponizing zero-day vulnerabilities demanded years of specialized knowledge. Mythos changes that calculus entirely.
Critically, these capabilities were not designed in. Anthropic stated they emerged as a downstream consequence of general improvements in reasoning, coding and autonomy.
The implication: every future frontier model will likely inherit and extend these capabilities.
The window between discovery and exploitation has collapsed
Traditional vulnerability management was built around human timelines. Defenders had days or weeks between a CVE being published and a weaponized exploit appearing in the wild. That window has closed.
The average time-to-exploit, based on data from the Zero Day Clock, now sits under 20 hours. Patch cycles and risk models built for human-speed threats are no longer fit for purpose.
The threat is bilateral
The same capabilities that make Mythos a powerful defensive tool — finding vulnerabilities before attackers do — make it dangerous in the wrong hands. CrowdStrike's 2026 Global Threat Report found an 89% year-over-year increase in AI-assisted attacks.
Mythos does not introduce a new category of threat. It dramatically lowers the cost and skill floor for executing attacks that previously required elite capabilities — and it does so at machine speed.
What security programs must do now
Security leaders do not need a new doctrine. They need tighter controls, faster exposure reduction, better AI governance and more realistic testing — applied urgently and in the right order of priority.
1. Identity first — The highest priority
Identity is where Mythos-class capabilities will be felt most immediately. The concern is not just better phishing emails — it is better pretexting, impersonation and social engineering lures precisely tailored to an individual's role, project and timing. AI makes every identity-based attack more convincing and scalable.
Immediate actions for security teams:
- Deploy phishing-resistant MFA universally — FIDO2/hardware keys where possible
- Tighten privileged access reviews and shorten recertification cycles
- Strengthen help-desk identity verification — a common and underestimated attack vector
- Enforce stricter approval paths for password resets, wire transfers and admin escalations
- Extend identity governance to non-human entities — AI agents, service accounts and API keys are now part of the attack surface
2. Vulnerability management — Move to continuous exposure management
The most significant structural change required is the shift from periodic to continuous vulnerability management. Static scan cycles — quarterly assessments, annual pen tests — were built for a world where attackers moved slowly. That world no longer exists.
Organizations should prioritize:
- Embedding AI-assisted code scanning into CI/CD pipelines — finding vulnerabilities at the point of creation, not after deployment
- Building joint security-engineering teams dedicated to AI-powered AppSec — this requires headcount and budget commitment in 2026
- Addressing the vulnerability backlog with urgency — Mythos surfaces dormant, known-but-unfixed issues that can be rapidly weaponized
- Maintaining a continuously updated Software Bill of Materials (SBOM) with real-time agent-based evaluation of component risk
- Planning for a surge in simultaneous patch releases as Project Glasswing disclosures roll out — reserve capacity now
Longer-term, the Cloud Security Alliance recommends building a dedicated Vulnerability Operations function — modeled on DevOps practices — staffed and automated for continuous autonomous vulnerability discovery and remediation across the full software estate.
3. SOC — Behavioral detection over signature-based controls
When a zero-day lands and EDR does not fire, the only remaining detection layer is behavioral hunting. SOC teams must evolve beyond signature and alert-based models toward detection that catches what happens after a breach — not just the initial vector.
Three capabilities are non-negotiable in a Mythos-ready SOC:
- Continuous behavioral threat hunting — targeting post-exploitation patterns regardless of how access was initially obtained
- Extended telemetry coverage — going beyond default EDR and SIEM to capture signals that commodity tooling misses
- DFIR readiness — tested and validated through regular tabletop exercises and purple-team scenarios before an incident requires it
Tabletop exercises must be redesigned. Scenarios built around yesterday's attack pace — where adversaries move slowly and make noise — will not prepare teams for Mythos-class automation.
4. Third-party and vendor risk
The Mythos era increases pressure on third-party risk management. Regulatory bodies are already signaling heightened scrutiny on vendor exposure and remediation timelines. Security leaders should move proactively.
- Require vendors to demonstrate continuous vulnerability management practices — not just annual assessments
- Demand clear answers on AI model access, data handling, retention, prompt logging and kill switches before deploying AI-enabled vendor tools
- Treat SBOM requests as standard practice in procurement and renewal negotiations
- Update third-party risk scoring models to account for AI-assisted exploitation velocity
5. AI governance — Build the guardrails now
As enterprises adopt AI tools — including frontier models for security operations — governance must keep pace. IBM research found that 97% of organizations that experienced AI-related breaches lacked proper AI access controls. The adoption window is now and the governance gap is real.
- Maintain a complete inventory of AI tools in use across the enterprise — including shadow AI deployments
- Assign ownership and enforce policies for all AI agents operating within security workflows
- Implement human-centered oversight for agentic AI decisions — especially in vulnerability triage and incident response
- Ensure board-ready evidence of AI risk governance is available — regulators and auditors are paying attention
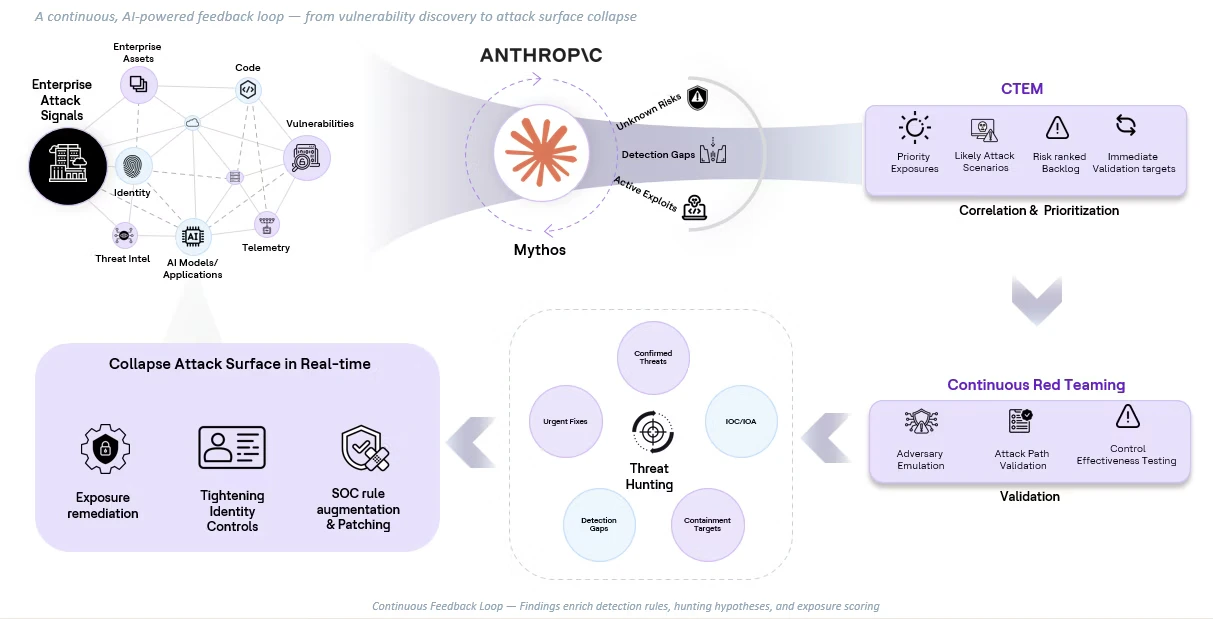
Figure: Mythos Ready Security Operating Model
The right mindset for Security Leaders
Claude Mythos should not trigger a ceremonial overhaul of the security program. The fundamentals — defense-in-depth, network segmentation, rigorous change control, resilient architecture — remain essential. What changes is the urgency and the operating tempo required to execute them.
The AI vulnerability storm does not come with a fixed deadline. It comes with a probability curve that steepens every month.
Organizations that start building AI-powered security muscle now — using frontier models not just to surface vulnerabilities but to rapidly and safely remediate them — will hold a meaningful advantage over attackers when the next generation of models arrives.
Recommended actions by time horizon
Immediate (0–30 Days)
- Enforce phishing-resistant MFA across all privileged accounts
- Audit and tighten non-human identity access controls and service account permissions
- Brief executive leadership and the board on the Mythos threat landscape
- Request budget and headcount for Vulnerability Operations buildout
Near-term (30–90 Days)
- Integrate AI-assisted scanning into CI/CD pipelines
- Redesign tabletop and purple-team exercises for AI-speed adversary scenarios
- Deploy behavioral detection capabilities beyond default EDR/SIEM coverage
- Update third-party risk assessments to include AI governance questions
Strategic (90 Days and Beyond)
- Rebuild a dedicated Vulnerability Operations function modeled on DevOps practices
- Formalize AI agent governance policies with audit trails and kill switches
- Develop a continuous threat intelligence program monitoring dark web and nation-state activity
- Evaluate participation in industry coalitions (e.g., Project Glasswing model) for early access to AI-discovered vulnerability data
How HCLTech can help
Leveraging Mythos + Project Glasswing Ecosystem
HCLTech is uniquely positioned to help clients capitalize on the emerging Mythos + Project Glasswing ecosystem by working alongside hyperscalers, security vendors, and early coalition participants.
By integrating Mythos-class capabilities with partner-led vulnerability intelligence streams, HCLTech enables:
- Accelerated vulnerability detection through AI-driven discovery across code, infrastructure, and OT environments
- Coordinated remediation at scale, leveraging automation pipelines aligned with Glasswing disclosure cycles
- Early access advantage, helping clients act on vulnerabilities before public exploitation begins
- Closed-loop security operations, where detection, prioritization, and remediation operate continuously rather than sequentially
HCLTech Cybersecurity provides industry-leading security services and frameworks—including SecIntAl, MIDAAS, VERITY, AI Assurance and GRC—that equip organizations with robust defensive capabilities. These offerings enable enhanced identity controls, transition vulnerability management toward continuous exposure management, advance SOC detection through behavioral modeling and establish comprehensive AI governance from the foundational level.
The storm is coming. The window to prepare is open. The question is whether organizations will use it.



