Multitenancy using network services extension projects and virtual private cloud: A modern networking model
As private clouds evolve to support diverse business units, partners and applications, multitenancy has become a foundational architectural requirement. Traditional approaches based on VLANs, shared Tier-0/Tier-1 gateways and extensive firewall rule sets often struggle to deliver the isolation, scalability and operational efficiency required for modern workloads.
With VMware network services extension (NSX), multitenancy has taken a significant step forward through the introduction of virtual private clouds (VPCs) and projects. Together, these capabilities deliver a cloud‑like consumption model within the data center, mirroring public cloud constructs such as AWS VPCs and Azure Virtual Networks.
This blog explores how NSX VPCs and projects enable secure, scalable and operationally efficient multitenancy and why they represent the future of private cloud networking.
Challenges with the traditional NSX multitenancy designs
Before the arrival of VPCs, NSX‑based multitenancy typically relied on shared Tier‑0 gateways, per‑tenant Tier‑1 gateways, logical segments per application, distributed Firewall (DFW) rule sets for isolation and RBAC applied at the vCenter/NSX global level.
While functional, the earlier model had several limitations. Shared routing domains reduce tenant isolation and increase the blast radius. Operational complexity was high, with central teams responsible for pre-creating and managing all networking constructs, resulting in poor self-service and a heavy reliance on administrators. As environments scaled, distributed firewall rules became increasingly complex, making them difficult to manage and audit. While functional, this earlier model had several limitations. NSX VPCs and Projects eliminate these limitations by redefining how tenants consume network services.
What is an NSX virtual private cloud (VPC)?
An NSX VPC is a logically isolated networking domain that provides tenants with dedicated IP address space, Routing domain, Segments, NAT and firewall boundaries.
Conceptually, an NSX VPC is similar to a public cloud VPC, but implemented entirely within NSX.
NSX VPCs are built on a provider gateway. They are fully isolated from other VPCs by default, while supporting both private and public subnets, enabling tenant-level NAT and routing and integrating natively with the NSX Distributed Firewall.
Each VPC functions as a self‑contained, tenant‑specific networking environment.
Provider gateways: The foundation layer
At the centre of the VPC architecture is the provider gateway, which forms the shared connectivity layer.
What is a provider gateway?
A provider gateway is a Tier-0–backed construct that connects multiple VPCs to external networks, enforces north–south connectivity policies and acts as a shared underlay for tenants. Unlike earlier shared Tier‑0 designs, Provider Gateways give infrastructure teams full control without exposing core networking complexity to tenants, enabling them to operate autonomously within their VPCs.
Projects: governance and consumption layer
While VPCs provide network isolation, projects provide organizational and governance boundaries.
What is an NSX project?
An NSX project is a logical container that groups one or more VPCs, policies, quotas and RBAC permissions.
Projects define who can create what and how much they can consume. It enables:
- Tenants-specific RBAC, allowing tenants to administer only their own resources
- Quota enforcement, controlling consumption (VPCs, segments, NAT rules, IP blocks)
- Delegated administration, giving tenants-controlled self‑service within guardrails
Full lifecycle management, enabling clean creation, modification and deletion of environments. This separation ensures that network operators focus on infrastructure, while tenants focus on applications.
VPC subnets and traffic models
Within a VPC, tenants can create subnets that map to logical segments, including private subnets with no direct external connectivity typically used for backend services and public subnets that provide NATed or routed access to external networks and are suitable for frontend workloads.
The traffic model distinguishes between east–west and north–south traffic flows. East–west traffic is fully distributed using the NSX Distributed Firewall, delivering high performance and low latency without centralized choke points. North–south traffic is controlled through the provider gateway, where VPC‑specific NAT and firewall rules are applied. This approach ensures clear separation and controlled handling of tenant traffic.
Security and isolation
Security is a core strength of NSX VPC‑based multitenancy. The distributed firewall (DFW) is enforced at the VM or workload interface, enabling tenant‑specific policies and zero‑trust segmentation within each VPC. Strong isolation boundaries ensure that VPCs cannot see or route to one another unless explicitly allowed, while projects enforce administrative separation. External access is centrally controlled by the provider gateway, resulting in a multi‑layered isolation model that significantly reduces operational and security risk.
Multitenant architecture with NSX projects and VPC
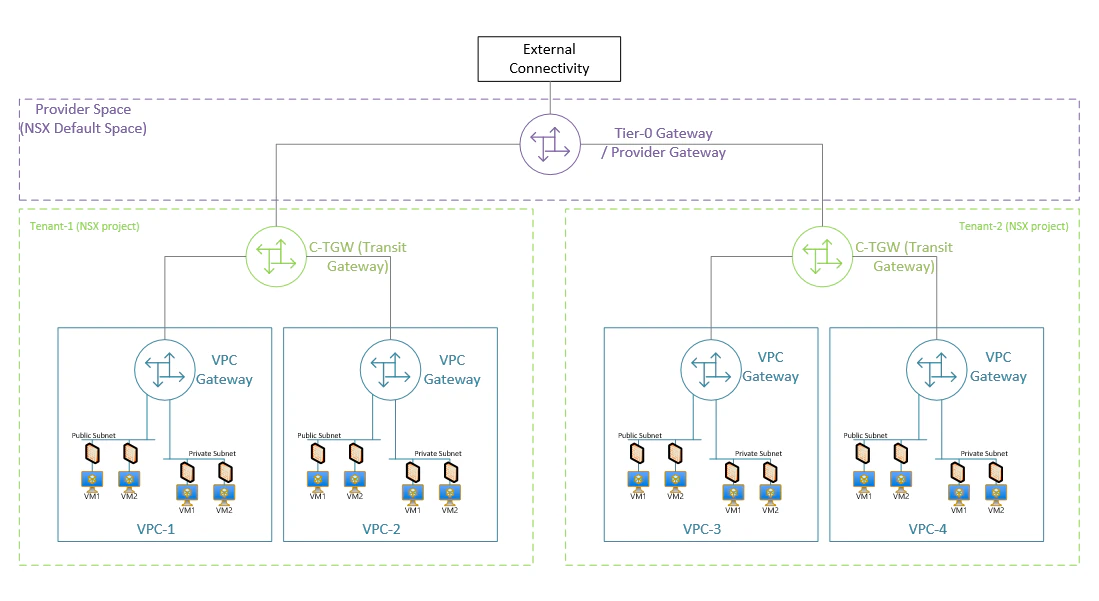
This diagram represents a multitenant private‑cloud networking architecture where multiple tenant VPCs (Tenant-1 and tenant-2) connect to external networks through a provider-managed Tier‑0 Gateway. Each tenant gets its dedicated transit gateway (C‑TGW) to isolate routing and enforce multitenancy.
Each tenant shown here has multiple VPCs (VPC-1 through VPC-4) each with dedicated VPC gateway and having private or public subnets.
Operational benefits for platform teams
From an infrastructure perspective, NSX VPCs and Projects deliver significant operational advantages. They reduce configuration overhead, enable a clear separation of duties and simplify troubleshooting, audits and compliance. Scalable tenant onboarding is achieved by allowing platform teams to define standardized network blueprints instead of building bespoke network designs for each tenant.
Customer use cases
NSX VPCs and Projects are ideal for enterprise private clouds, service providers and large organizations with multiple business units. These are also well-suited for Dev/Test and multi‑environment setups, as well as regulated environments that require strict isolation and strong governance controls.
Conclusion
NSX VPCs and Projects represent a significant advancement in private cloud networking. By abstracting underlying complexity, providing robust isolation and facilitating self-service within defined parameters, these solutions integrate public cloud operational models into the data center.
For organizations modernizing their infrastructure or building internal cloud platforms, adopting NSX VPC–based multitenancy is a critical step. As private clouds continue aligning with public cloud paradigms, NSX VPCs and Projects provide a secure, scalable and future‑ready framework for multitenancy.