Many organizations have begun to experience business disruptions or outages due to incidents at their third-party organizations. These incidents can range from outages to cybersecurity breaches. In recent years most customers have found the challenge of managing the cybersecurity of their own infrastructure less daunting than before. However, they continue to struggle with protecting themselves from risks introduced by their third-party ecosystem and managing cyber resiliency. This struggle has intensified as the attack surface has expanded due to outsourcing.
The urgent need of the hour is to understand the approaches and best practices for integrating your business resiliency plan with third-party risk management. This integration can help your organization moderate the impact of disruptions that may occur in a third-party environment.
Impact of third-party risk on organizational business resilience
Today's industry understands the benefits of outsourcing which has led to a heavy dependency on third parties. Because of this dependency organizations are sharing more data and information with their third parties. This kind of exposure shifts the risk management dynamics.
If third parties do not have proper business resiliency arrangements, they can significantly impact organizational business resilience. It's also important to understand the growing dependence on third parties to achieve business objectives. Organizations now demand uninterrupted services within agreed service level agreements from their third parties. These services must incorporate robust data security privacy and business resiliency practices.
A daunting question for many organizations is how to design and operate an organizational business resiliency program amidst the risks introduced by third-party relationships. Events such as natural disasters or cybersecurity incidents at a third party can introduce unexpected disruptions to an organization's business activities and objectives.
Integrating business resiliency and TPRM
Unfortunately, only a handful of organizations have made reasonable efforts to manage their third-party relationships from a business resiliency standpoint. When considering their own business continuity planning these organizations have covered not only their own ability to overcome disruptions but also the resilience of their third-party ecosystem. They have achieved this by establishing efficient and effective collaboration.
Integrating cyber resilience and TPRM makes complete sense. Organizations have started leveraging third parties aggressively to support IT infrastructure or application management cloud service offerings data management non-IT services and products and many other needs.
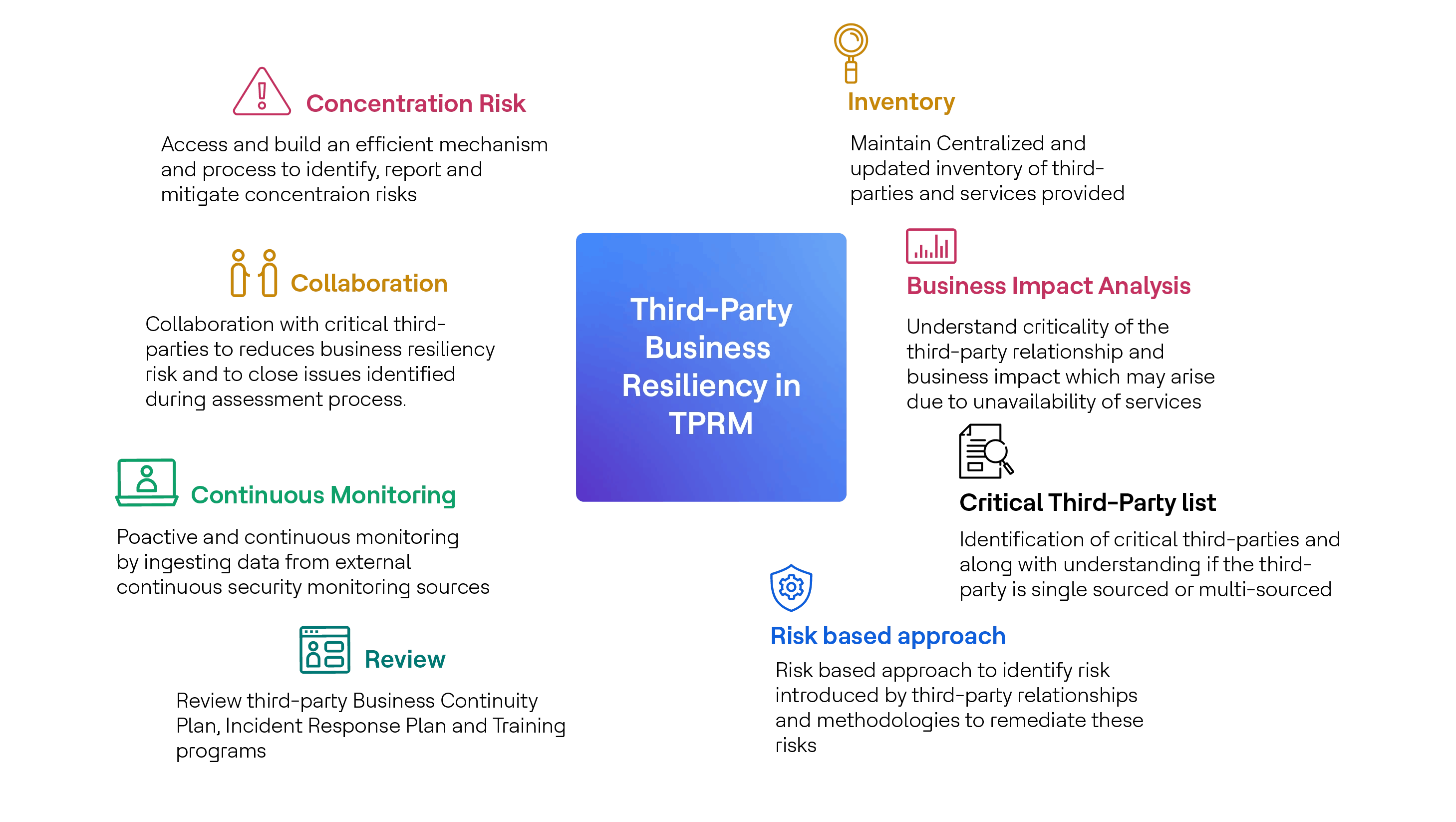
Organizations need to focus on several key areas:
Keeping an up-to-date inventory of third parties to understand sources of risks identify and remediate risks categorize third parties monitor third-party performance and manage the mapping of services provided by third parties to organizational business processes.
Performing a Business Impact Analysis to understand the criticality of the third-party relationship and the business impact that may arise due to the unavailability of services provided by third parties.
Identifying critical third parties and the services they provide along with understanding if the third party is single-sourced or multi-sourced.
Determining the risks introduced by third parties can be complex. There is no one-size-fits-all solution since the risk introduced by every third party can be different and needs to be assessed accordingly. Designing a risk-based approach is the right way to identify the risk introduced by each third-party relationship. This approach should cover the main risk factors for the organization to identify and assign risk ranking to third parties develop risk categories/ratings and establish a risk treatment methodology.
Reviewing and validating a third party's Business Continuity Plan Incident Response Plan and Training and Awareness programs.
Proactively and continuously monitoring data from external continuous security monitoring sources such as SecurityScoreCard, BitSight and UpGuard.
Establishing collaboration mechanisms with at least critical third parties. By doing this an organization may be able to reduce business resiliency risks arising from third-party outages and assess vendors' business resilience plans. This will also help in closing the gaps identified during the assessment process.
Including the right Contract Security Clauses. These should include requirements around Business/Cyber resiliency in third-party contracts along with certain mandates such as the right to audit security requirements service level agreements and performance monitoring indicators.
Building an efficient mechanism and process to identify report and mitigate concentration risks. Concentration risk should be seamlessly integrated with the inherent and residual risk processes.
Concentration risk can introduce service outages and disruptions to services provided by third parties. Developing and implementing business resiliency mechanisms associated with third parties can be challenging. These mechanisms may contradict an organization's strategic efforts to leverage single-source suppliers. However, it is crucial for the responsible team to keep the organization's senior management informed so that strategic initiatives can be modified or adjusted to reduce single points of failure and third-party concentration risks.
Conclusion
In the evolving landscape of digital business, cybersecurity has been the cornerstone of any robust TPRM program. Yet, as we navigate through increasingly complex networks of third-party relationships, the lens through which we view risk management must expand. Business resiliency has emerged as a critical component that demands our attention.
The integration of business resiliency into your TPRM program is not just a necessity, but a strategic move. It empowers organizations to identify, manage and measure third-party concentration risks, providing a comprehensive view of potential vulnerabilities. It's about proactively addressing business resiliency risks introduced by third-party relationships, enhancing efficiency and ensuring timely responses. This approach also paves the way for the maturation of your Business Continuity Management program, fostering a culture of continuous improvement. It invites a reevaluation of your strategic direction for third-party relationships, encouraging adaptability in the face of change.
It is key to remember that third parties are not merely external entities, but extensions of your own organization. The risks they present - be it technology/cyber risk, concentration risk, financial viability, operational (business resiliency) risk or reputational risk - are your risks. Therefore, their business resiliency and disaster recovery plans must be woven into the fabric of your TPRM program. This holistic approach is the key to building a resilient organization that can thrive amidst uncertainty.


