Accelerate Your Digital Transformation
We help businesses adopt digital technologies at the core of business transformation, which includes a combination of core infrastructure services and next-generation digital services that pivot around hybrid cloud, digital workplace, software-defined networking, cybersecurity, unified service management and intelligent operations. Our clients leverage these services to develop long-term digital transformation strategies to meet their current and future needs.

We think these topics might interest you
IT Infrastructure Solutions to Maximize Value for Long-term Success
HCLTech's suite of cloud & infrastructure managed services spans management, hosting, migration, and evolution of your infrastructure, catering to both on-premises and cloud environments.

Hybrid Cloud Services
Our next-generation data centers with autonomics and orchestration capabilities aid in creating unified experiences.

Digital Workplace Services
Our digital workplace strategy, solutions and services bring together technology, people and culture to build a workplace that boosts productivity, engagement and positivity.

NextGen Networks
We enable business transformation and strategic alignment of next-gen enterprise networks, making them lean, agile, experience-centric and outcome-based.

Fluid Contact Center (FluidCC)
FluidCC offers comprehensive technology services and accelerators for contact center digital transformation and assists enterprises in re-imagining their customer service experience by creating AI-powered customer journeys.

Cybersecurity
We help companies Identify, understand and manage security, risks and compliance.

Digital Foundation Consulting
We enable organizations benefit from the right technologies with our approach to digital solutions, people and processes that come together – transforming them into resilient and adaptive enterprises.

Service Integration & Management
We design and build the right SIAM model using our accelerators while implementing and integrating multiple vendors.

Autonomics Services
Transforming IT with NoOps powered by HCLTech Intelligent Operations Platform which is AI-first full stack integrated offering aimed at organizations that require an infusion of advanced AIOps to boost their operations ecosystem.

Infrastructure Modernization Services
End to end AI powered IT modernization services to drive business agility
Digital Infrastructure Solutions to Make Your Enterprise Thrive
Empower your enterprise with our range of cutting-edge digital infrastructure solutions. From optimizing cloud environments to enhancing network reliability and security, we offer comprehensive solutions to drive your business forward.
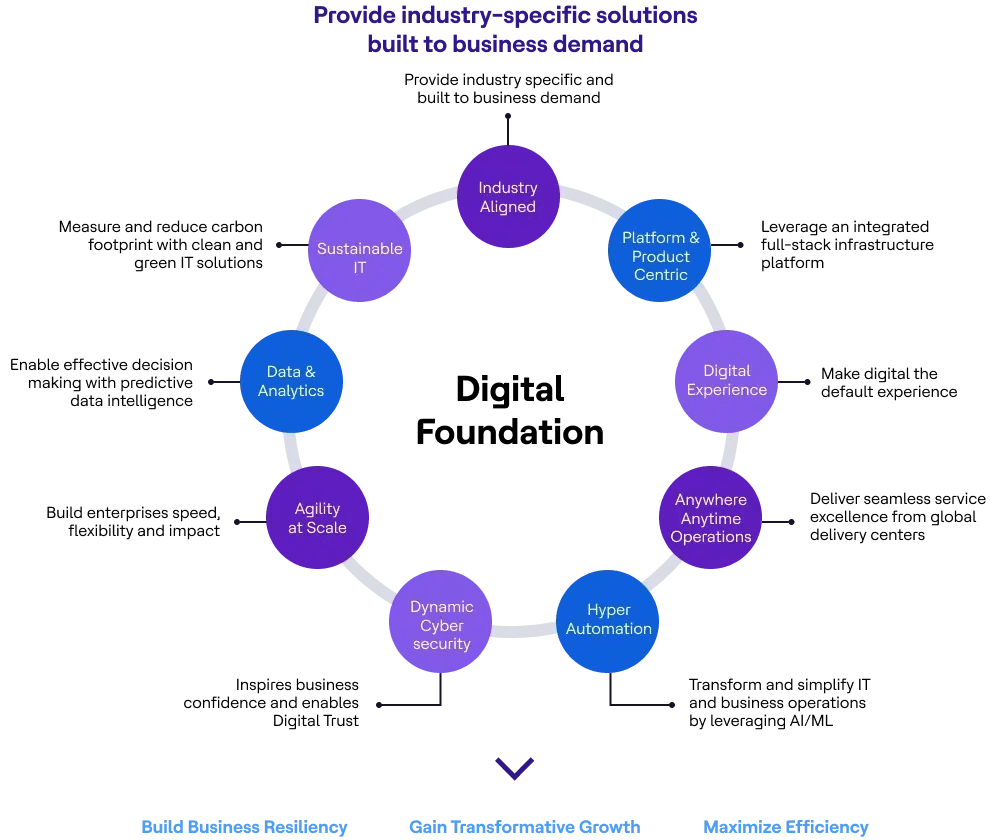
Build a Strong Digital Foundation for Your Enterprise with HCLTech
Frequently Asked Questions about Our Digital Foundation Services
HCLTech’s Digital Foundation service delivers resilient, adaptive IT infrastructure management services designed to help clients transform their digital journeys. We combine core IT infrastructure solutions with advanced digital technologies—covering cloud, networks, security and intelligent operations—to build a robust platform that drives business growth and operational excellence.
Our Digital Foundation framework delivers three key benefits: resiliency to keep operations running smoothly, transformative growth to enable digital-first business models and maximum efficiency through automation and cost optimization. We help clients achieve agile delivery, improved customer experiences and measurable business results—proven through real-world success stories.
We begin with a comprehensive infrastructure maturity assessment, leveraging our consulting expertise and proven methodologies. By evaluating your current IT landscape, processes and business goals, we identify gaps and opportunities. This helps us tailor a digital foundation roadmap that aligns with your unique transformation objectives and industry best practices.
Yes, our solutions are built for seamless integration with your existing IT systems. We take a vendor-agnostic, flexible approach—leveraging our deep experience across diverse technology stacks. This ensures minimal disruption, protects your technology investments and enables a smooth transition to a modern digital foundation.
Yes—our digital foundation solutions are engineered to support global operations at enterprise scale. We have extensive experience managing complex, distributed IT environments for multinational clients, ensuring consistent performance, security and compliance across regions. Our global delivery model guarantees reliable support wherever your business operates.
We support enterprise digital transformation by integrating modern digital technology services with proven IT infrastructure management. Our approach blends hybrid cloud, digital workplace, next-gen networks and cybersecurity to create agile, future-ready environments. Clients benefit from our experience in delivering scalable, secure solutions that accelerate innovation and drive lasting business outcomes.
We cover the entire IT infrastructure landscape—hybrid cloud, digital workplaces, networks, cybersecurity, service integration, autonomics and modernization. Our solutions span on-premises and cloud environments, ensuring seamless operations, robust security and continuous optimization so clients can confidently navigate complex digital transformation challenges.
Absolutely—our digital foundation is designed for hybrid and multicloud environments. We use advanced orchestration, automation and security frameworks to unify on-premises and cloud resources. Clients gain flexibility, scalability and control, ensuring their infrastructure supports both current needs and future growth across any cloud model.
Every client’s needs are unique, so we tailor our digital foundation framework to fit your specific business objectives, industry requirements and operational priorities. Our consultative approach and modular solutions allow us to design, implement and manage IT infrastructure that aligns perfectly with your growth strategy.
We build resiliency into every layer of your IT infrastructure by combining proactive monitoring, automation and robust security practices. Our intelligent operations platform enables rapid incident response and self-healing capabilities. Clients benefit from minimized downtime, business continuity and the confidence to adapt to changing conditions or disruptions.